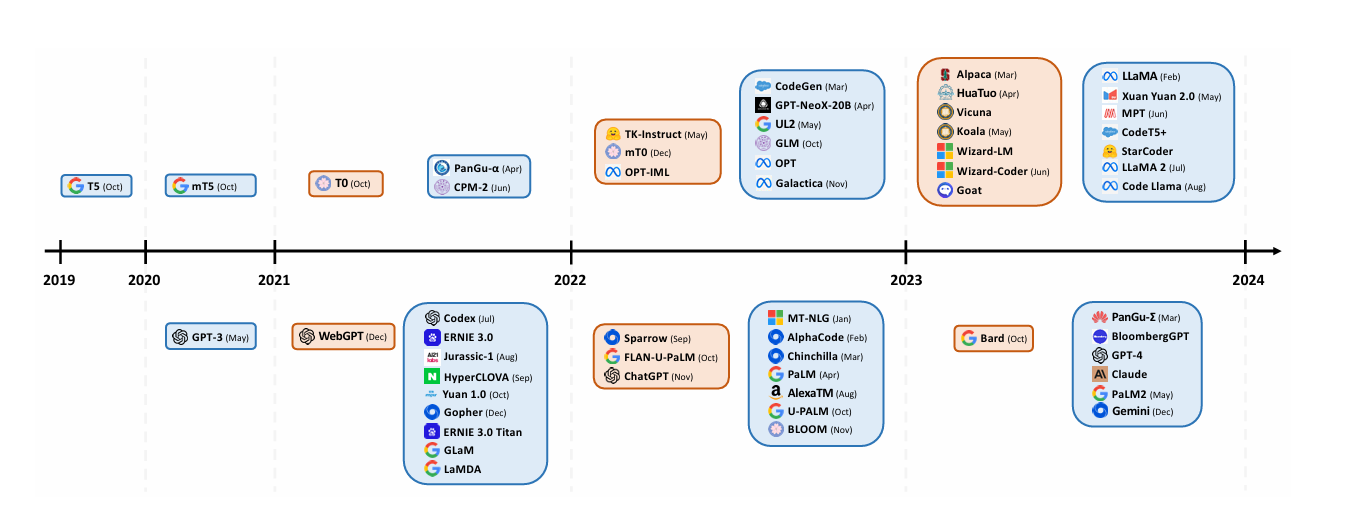
This paper provides a comparative analysis of the systematic security capabilities of four leading large language models: OpenAI's ChatGPT, Meta AI’s LLaMA, Moonshot AI's BERT Chat, and Baidu's ERNIE series, including "Wenxin Yiyan." Each model's performance in addressing potential systematic security threats and vulnerabilities was evaluated through a rigorous assessment process. The study found significant differences in the security performance of these models. Specifically, ChatGPT exhibits remarkable resilience in handling confidential information, while LLaMA's advanced contextual understanding enhances its ability to identify and mitigate emerging security risks. BERT Chat stands out due to its strong user privacy protections, and Baidu's ERNIE, particularly "Wenxin Yiyan," provides comprehensive data security through multiple layers of defense. The study highlighted the diversity of security strategies employed by models, while pointing to the need for continued innovation in security measures as large language models develop.